Solana DeFi is routinely described as permissionless. The claim is technically accurate at one layer of the stack — and quietly misleading at every layer above it. Understanding where access is genuinely open and where it is filtered, screened, or blocked is not an academic exercise. It is the difference between knowing what you own and knowing what you can actually use.
Table of Contents
- The Stack Nobody Draws: Four Layers, Four Different Access Rules
- The Frontend Is Not the Protocol: Where Access Actually Gets Blocked
- The Validator Blacklist: A Second Access Filter Operating Below the Surface
- The CLI Escape Hatch: Protocol Access Without the Interface
- What “Permissionless” Actually Promises — and What It Doesn’t
The Stack Nobody Draws: Four Layers, Four Different Access Rules
When participants say Solana DeFi is permissionless, they are usually describing the protocol layer: smart contracts that execute deterministically for any valid transaction, without asking who sent it. This is real. The Solana Labs Stake Pool Program that underpins JPool’s architecture, for instance, has no mechanism to identify or reject a user — it processes valid on-chain instructions, period.
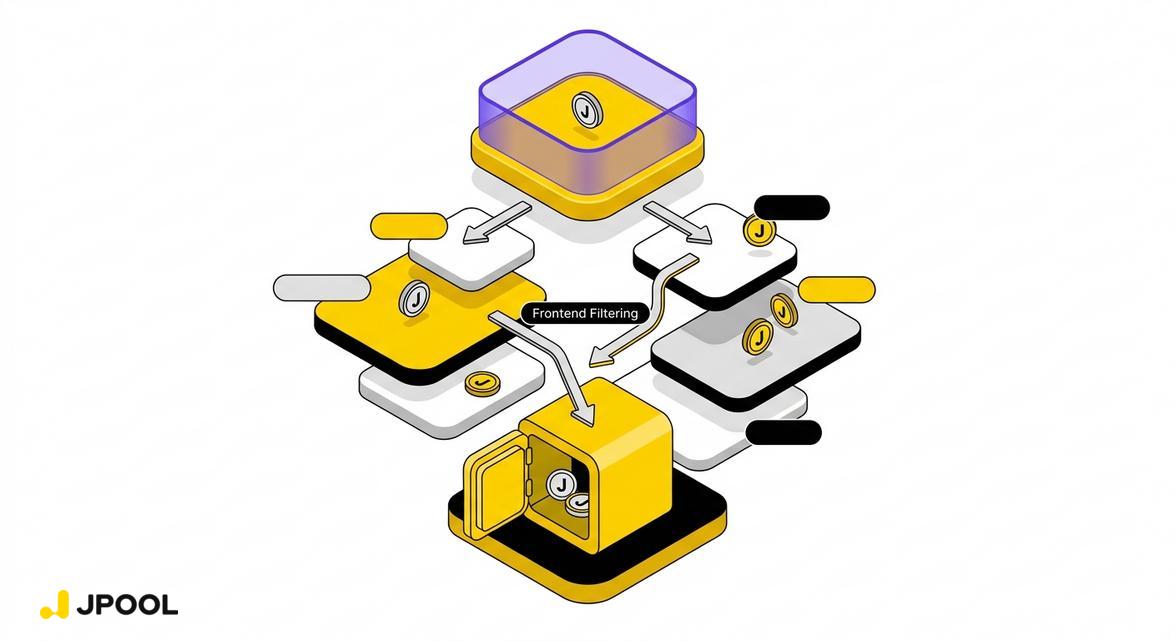
But most users never interact with the protocol layer directly. They interact through a stack of intermediaries, each of which applies its own access logic:
- The Protocol Layer — Smart contracts on-chain. Genuinely permissionless: no identity check, no geographic filter, no wallet screening. Any valid transaction executes.
- The Interface Layer — The frontend web application (e.g., jpool.one). Subject to Terms of Service, geographic IP filtering, and wallet address screening.
- The Validator Layer — The nodes that process and order transactions. Subject to blacklisting by ecosystem bodies and exclusion from delegation programs.
- The Compliance Layer — OFAC, EU, and international sanctions frameworks that legally obligate service providers to restrict access.
The permissionlessness of layer one does not cascade upward. Each layer above it introduces its own gatekeeping logic — and most users operate exclusively at layers two through four.
The Frontend Is Not the Protocol: Where Access Actually Gets Blocked
JPool’s Terms of Service make the interface-layer reality explicit. Users from jurisdictions subject to OFAC sanctions, EU restrictions, and other international frameworks — including Afghanistan, Belarus, Cuba, North Korea, Iran, Russia, Syria, Sudan, and the Crimea region of Ukraine — may not access or use JPool’s Services. JPool reserves the right to update this list and refuse service to wallet addresses from restricted regions as required by international law. If a wallet is found to be associated with a restricted region, access may be blocked or suspended immediately.
This is not unique to JPool. It is the operational reality of any frontend that serves users through a web interface with identifiable wallet addresses. The moment a service provider can associate a wallet address with a jurisdiction or a sanctioned entity, the compliance obligation activates — and the frontend becomes a gate, not a door.
The critical distinction: the underlying smart contract does not enforce these restrictions. JPool’s documentation is unambiguous that it uses Solana Labs’ Stake Pool Program for all operations with funds, and that JPool has no access to user SOL whatsoever. The protocol layer remains open. The interface layer is where the filtering occurs.
This creates a structural asymmetry that most DeFi commentary ignores: a user whose frontend access is blocked still holds their JSOL tokens. The tokens are on-chain. The protocol will still process valid instructions. But without interface access, the practical ability to manage, redeem, or deploy those tokens is severely constrained for most users.
The Validator Blacklist: A Second Access Filter Operating Below the Surface
The frontend is the visible access gate. There is a second, less-discussed filter operating at the validator layer: blacklisting.
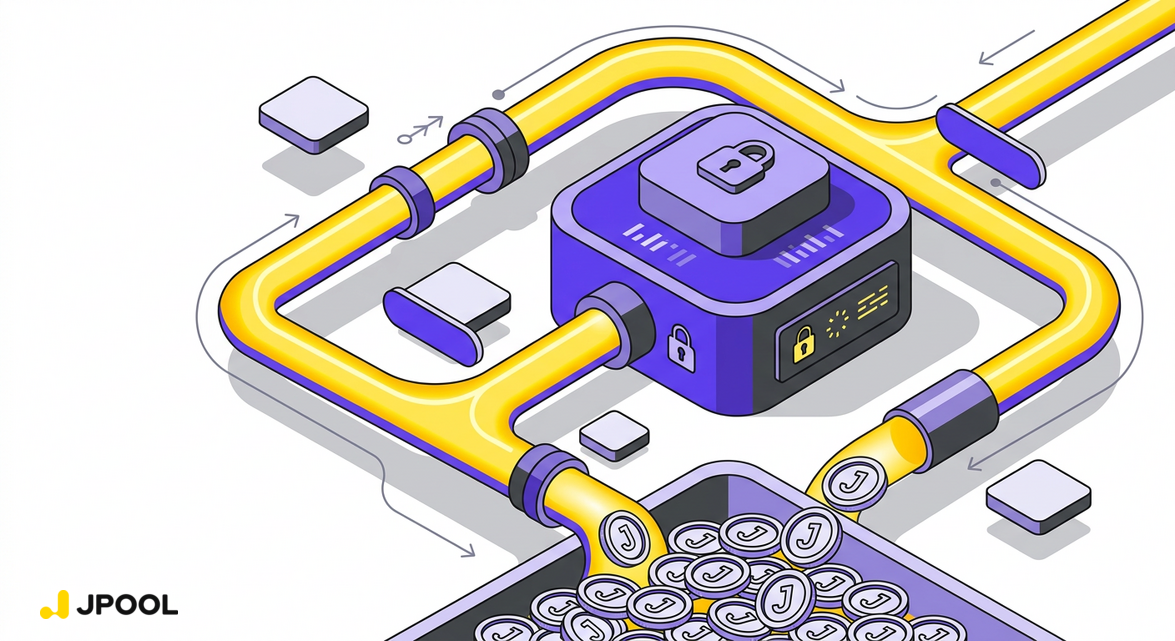
JPool’s delegation program eligibility criteria are explicit: every validator in the program must not be on any blacklist — specifically the Solana Foundation blacklist, the Jito Foundation blacklist, or JPool’s internal blacklist. A validator that appears on any of these lists is immediately removed from the program. The trigger is automatic: being added to a blacklist is listed as one of the conditions for instant removal.
This matters for the permissionlessness question in a specific way. Validators process and order transactions on Solana. A validator that is excluded from major delegation programs faces economic pressure that can affect its operational viability. And if a validator chooses to filter or deprioritize certain transactions — a behavior that is technically possible at the node level — users whose transactions are routed through that validator may experience de facto censorship without any on-chain mechanism enforcing it.
The Solana network’s design assumes that a sufficient number of independent validators will process any valid transaction. But the composition of the active validator set — which validators receive stake, which remain economically viable, and which are excluded from delegation programs — directly shapes whether that assumption holds in practice. Delegation programs like JPool’s, which explicitly exclude blacklisted validators, are simultaneously a decentralization mechanism and a censorship-resistance mechanism: by distributing stake broadly to non-blacklisted, non-superminority validators, they reduce the probability that any single filtered node controls a meaningful share of transaction ordering.
The CLI Escape Hatch: Protocol Access Without the Interface
Advanced users who understand the stack separation have a practical option that most documentation buries: direct CLI interaction with the underlying program.
JPool’s CLI reference documents command-line operations for deposits, withdrawals, and bond management using the spl-stake-pool CLI from the Solana Program Library. This path bypasses the web frontend entirely. A user who can construct and sign valid on-chain transactions — using spl-stake-pool withdraw-sol or spl-stake-pool deposit-sol — is interacting directly with the protocol layer, where the permissionlessness is genuine.
This is not a workaround for sanctions compliance — JPool’s Terms of Service obligations apply regardless of how the platform is accessed, and users remain bound by applicable law. But it illustrates the architectural point precisely: the protocol and the interface are separate systems with separate access rules. The CLI path exists because the protocol is open; the frontend path is where the compliance layer applies.
JPool maintains a minimum reserve of 0.5% of TVL (at least 5,000 SOL) to ensure withdrawals are always possible — a design choice that keeps the protocol-layer exit route liquid even when interface access is unavailable.
What “Permissionless” Actually Promises — and What It Doesn’t
The honest framing of Solana DeFi permissionlessness is this: the protocol layer will execute any valid instruction from any valid keypair. That is a meaningful guarantee. It means no central party can unilaterally freeze assets at the smart contract level, alter the exchange rate, or prevent redemption by modifying the on-chain program.
What it does not guarantee: uninterrupted access through any specific interface, freedom from compliance obligations that apply to service providers, or immunity from the economic and reputational pressures that shape which validators remain viable.
For users engaging with liquid staking infrastructure like JSOL — which sits inside an increasingly interconnected Solana financial stack spanning staking, lending, liquidity provision, and leveraged positions — understanding this distinction is operationally significant. The DeFi composability loops built on JSOL assume interface access. The next-generation yield layers emerging from restaking and shared security introduce additional protocol dependencies. And redemption liquidity mechanics operate differently depending on whether a user can access the interface or must fall back to direct protocol interaction.
JPool’s non-custodial architecture — where the platform has no access to user SOL and all fund operations run through the audited Solana Labs Stake Pool Program — represents the strongest available design response to this reality. It ensures that the protocol-layer guarantee is real: no JPool action can block a user’s on-chain assets. But it cannot extend that guarantee upward into the interface, compliance, or validator layers, where access rules are set by legal frameworks and ecosystem governance rather than by code.
That is the illusion of permissionlessness: not that the promise is false, but that it applies to a narrower slice of the stack than most participants assume. Knowing exactly which layer you are operating at — and what access rules govern it — is the prerequisite for making informed decisions in Solana DeFi.
Explore JPool’s non-custodial liquid staking architecture at jpool.one.
Subscribe to our digest pages and stay updated:

Leave a Reply