Solana’s throughput is its defining competitive advantage. It is also, in specific DeFi contexts, a structural vulnerability surface that most liquid staking discussions have not yet addressed directly.
Table of Contents
- Why Solana’s Throughput Creates a Unique Oracle Attack Surface
- The TWAP Failure Window: From Price Dislocation to Forced Liquidation
- Spot Price vs. Exchange Rate: Why JSOL’s Pricing Mechanism Is Structurally Different
- The Suspicious APY Drop Flag: An Underappreciated Early-Warning Layer
- What Resilient Liquid Staking Infrastructure Actually Means for DeFi Collateral
The same sub-400-millisecond block times that make Solana attractive for high-frequency trading and real-time DeFi create a narrow but exploitable window: the gap between when a price moves on-chain and when an oracle feed updates to reflect it. In low-latency environments, that gap is not a rounding error. It is the attack surface.
This article examines how oracle manipulation operates in Solana’s latency environment, why TWAP-based price feeds fail under targeted conditions, and what properties of liquid staking infrastructure — specifically JSOL’s architecture — create structural resistance to liquidation cascades triggered by oracle exploits.
Why Solana’s Throughput Creates a Unique Oracle Attack Surface
Traditional blockchain oracle manipulation is constrained by block times. On slower networks, the cost of holding a manipulated price for multiple blocks — paying gas across each one — makes sustained manipulation economically prohibitive for most targets.
Solana’s architecture changes this calculus. With block times measured in milliseconds rather than seconds, a sophisticated actor can execute a sequence of transactions — a large spot trade to move price, a liquidation call against a position using the manipulated price, and a reversal trade — within a window so narrow that TWAP-based oracles cannot register the dislocation as a sustained price move.
This is the core of the low-latency oracle manipulation problem: TWAP feeds are designed to smooth out noise over time, but on Solana, “over time” can be measured in hundreds of milliseconds. A price spike that lasts three blocks on Solana may be invisible to a TWAP window calibrated for slower networks — yet it can be sufficient to push a collateralized position past its liquidation threshold.
The result is a class of exploit that does not require breaking any protocol. It requires only that the attacker understands the oracle’s update frequency better than the protocol’s liquidation engine does.
The TWAP Failure Window: From Price Dislocation to Forced Liquidation
Time-Weighted Average Price feeds are the standard defense against spot price manipulation in DeFi. The logic is sound: averaging price over a window makes single-block manipulation prohibitively expensive. But TWAP’s effectiveness is a function of the ratio between the manipulation window and the TWAP window.
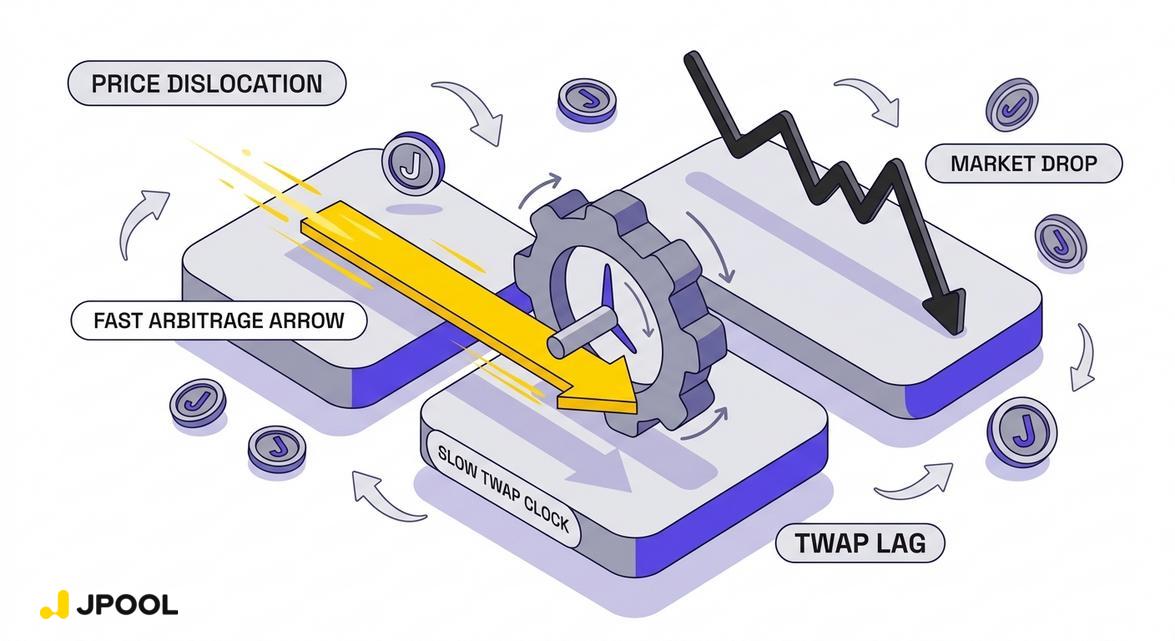
On Solana, this ratio is compressed. Consider the sequence:
- Price dislocation: An actor executes a large market sell on a thin liquidity pool, moving the spot price of an asset downward by a material percentage within a single block.
- TWAP lag: Because the TWAP window has not yet incorporated sufficient post-dislocation blocks to average the price back toward fair value, the oracle feed reflects a price meaningfully below the true market price.
- Liquidation trigger: A lending protocol using this oracle feed calculates that a collateralized position has crossed its Loan-to-Value threshold. The liquidation engine fires.
- Reversal: The attacker reverses their initial trade, capturing the liquidation bonus and restoring the price — all within a window that may span only seconds.
The critical vulnerability is not the TWAP mechanism itself. It is the assumption that the TWAP window is long enough relative to block time to absorb manipulation. On Solana, that assumption requires explicit calibration. Protocols that import TWAP parameters from slower-chain deployments without recalibrating for Solana’s block cadence are operating with a misconfigured defense.
For users with collateralized DeFi positions — including those using liquid staking tokens as collateral — the consequence is asymmetric: the attacker profits from the liquidation bonus, the liquidated user loses collateral, and the oracle feed may return to fair value before any on-chain record of the manipulation is legible as such.
Spot Price vs. Exchange Rate: Why JSOL’s Pricing Mechanism Is Structurally Different

The oracle manipulation risk described above applies most acutely to assets whose collateral value is determined by spot price feeds. This is where JSOL’s pricing architecture diverges from the standard model in a way that has direct implications for low-latency DeFi risks.
JSOL does not accrue value through a spot price that can be moved by a single large trade. Its value is determined by the JSOL↔SOL exchange rate — the ratio of total staked SOL plus accumulated rewards to total JSOL supply. As JPool’s documentation states: “Rewards are compounded by increasing the SOL-per-JSOL exchange rate over time. Your number of JSOL stays the same; each JSOL is simply redeemable for more SOL later.”
This exchange rate is updated at the epoch boundary — approximately every two days — not by real-time market activity. It cannot be moved by a single block’s worth of trading volume. An actor who executes a large JSOL spot sale on a DEX moves the DEX pool price, but does not change the underlying exchange rate that determines JSOL’s fundamental redemption value.
For lending protocols that price JSOL collateral against its exchange rate rather than its DEX spot price, this creates a meaningful structural defense: the collateral value of JSOL is epoch-anchored, not block-anchored. The manipulation window that enables low-latency oracle exploits against spot-priced assets does not apply in the same way to an asset whose fundamental value updates on a two-day cycle.
This does not make JSOL immune to all oracle risk — DEX-based price feeds for JSOL can still diverge from the exchange rate during periods of thin liquidity. But it means that the specific attack vector of sub-second price dislocation triggering liquidation is structurally harder to execute against JSOL collateral than against assets with purely spot-based pricing.
The Suspicious APY Drop Flag: An Underappreciated Early-Warning Layer
Beyond the token’s pricing architecture, JPool’s validator monitoring system contains a mechanism that functions as an indirect defense against a related class of risk: sudden, unexplained performance anomalies that can signal validator-level compromise or manipulation.
JPool’s documentation specifies that a validator is flagged as suspicious if it exhibits a suspicious APY drop of more than 20% relative to the previous epoch — unless the validator’s bond health is at 100%, in which case a fully funded bond exempts the validator from this check. A very suspicious APY drop — defined as an absolute change exceeding 50% — triggers instant removal from the delegation program.
This mechanism matters in the oracle manipulation context for a specific reason: validators with degraded performance can affect the accuracy of on-chain yield data that downstream protocols may use to price staking derivatives. A validator that suddenly underperforms — whether due to technical failure, targeted attack, or deliberate commission manipulation — creates a discrepancy between the staking yield that JSOL’s exchange rate reflects and what a naive external observer might calculate from raw validator data.
By flagging and removing anomalous validators before their performance degrades the pool’s aggregate yield, JPool’s monitoring layer reduces the surface area for yield-data manipulation that could affect how JSOL is priced or valued in external systems.
It is also worth noting that JPool uses a 95% credits ratio threshold when calculating its Target APY benchmark — the reference yield that the bond system guarantees to stakers — filtering out validators with poor vote participation from that calculation. This ensures the benchmark itself is not distorted by validators with degraded block participation, which could otherwise cause the guaranteed yield floor to be set against an artificially low reference point.
What Resilient Liquid Staking Infrastructure Actually Means for DeFi Collateral
The oracle manipulation risk described in this article is not hypothetical. It is a known attack vector that has affected DeFi protocols on multiple chains, and Solana’s latency profile makes it a particularly relevant concern for any collateralized position.
For users evaluating liquid staking tokens as DeFi collateral, the relevant question is not just “what yield does this token earn?” It is: “how is this token’s collateral value determined, and how resistant is that determination mechanism to low-latency manipulation?”
JSOL’s epoch-anchored exchange rate, combined with JPool’s bond-backed yield floor and real-time validator anomaly detection, creates a collateral profile that is structurally more resistant to the specific oracle attack vectors that Solana’s speed enables. The bond system — where validators post collateral covering both security risks and APY shortfalls — means that JSOL’s exchange rate growth is not dependent on any single validator’s real-time performance. Even if individual validators are flagged, suspended, or removed, the pool’s aggregate yield trajectory remains protected by the bond mechanism.
This is the layer of liquid staking infrastructure that most discussions of the Solana DeFi stack’s convergence do not surface explicitly: the structural properties of a liquid staking token’s pricing mechanism are a DeFi risk parameter, not just a yield parameter. In a low-latency environment where oracle manipulation is a live attack vector, the difference between a spot-priced asset and an epoch-anchored staking derivative is the difference between a liquidation target and a resilient collateral position.
Liquid staking infrastructure that operates with audited non-custodial architecture, epoch-based exchange rate settlement, bond-backed yield guarantees, and real-time validator anomaly detection is not simply offering better staking yield. It is offering a fundamentally different risk profile for every DeFi position built on top of it.
Explore JPool’s liquid staking infrastructure and start building a more resilient DeFi position at jpool.one.
Subscribe to our digest pages and stay updated:
Facebook Community · Instagram · Threads · Pinterest
Leave a Reply